Google’s Gmail is one of the most incredible email providers on earth, with more than one billion users regularly looking into their protecting Gmail accounts. You can utilize Gmail either as an individual account or as a feature of a G Suite account, which accompanies Hangouts, Google Tasks, Google Keep, and Google Calendar if you utilize your Gmail for business as a component of a team, you likely have the last option. Any way you use Gmail, losing access ensuing to forgetting your login details – or being hacked due to a weak password could have huge implications for you really and as a business. Let us perceive how you can protect your Gmail account.
A safe password is an initial phase in protecting your Gmail account and your information, and you should update it routinely, guaranteeing that it’s difficult to figure and not currently being used for any of your other apps or accounts.
What we will see here?
Passwords and Protection
Avoid Obvious Passwords for Gmail
The difficulty is, probably the most straightforward passwords to remember are likewise the absolute least secure. Attempt to try not to utilize passwords that are moreover:
- Your partner’s name
- Child’s name
- Pet’s name
- Your address
While these kinds of passwords are not difficult to remember, the data is additionally genuinely straightforward for a hacker to discover. At times, like your address data, it might even be a public record. If a hacker figures out how to get into your social media account, they can likely likewise become familiar with the names of those near you.
Passwords that others normally use are additionally bad decisions. They are among the first that a hacker would attempt to get to your account with. One security organization, Splashdata, really keeps a list of a portion of the worst passwords that people use by year. Their most recent list incorporates usually utilized passwords such as:
- 123456
- abc123
- password
- welcome
A portion of these is the default passwords that numerous systems accompany. If you perceive your password on one of their lists, change it right away.
Choose a Longer, Random Email Password
The best passwords are random and contain different kinds of characters. For instance, a password that contains upper and lowercase letters, numbers, and symbol is harder to hack than a password, everything being equal, or numbers.
Additionally, the more drawn out the password, the harder it is to hack. Passwords ought to be somewhere around eight characters in length. Some experts specialists suggest utilizing at least twelve or more characters.
Avoid independent online password generators since the webpage might be attempting to harvest passwords. A password generator remembered for a trustworthy security tool is probably protected though.
Once you track down a decent password, you might be tempted to utilize it for every one of your accounts. Try not to do it. If your password becomes compromised, then, at that point, the hacker possibly approaches your whole online presence.
Some of the attributes that make your password difficult to figure, likewise make it harder to remember. That is the reason thought of a secure way to store your passwords.
Store Your Gmail Passwords Securely
Having a secure Gmail password is nothing but bad if hackers can without much of a stretch find down it.
Utilizing Your Email Password on a Public PC: If you do utilize your password on a public device, clear the cache and memory a short time later. You may likewise wish to change your password.
Keeping Your Password on Your Person: Writing your passwords on a sheet of paper and keeping it in your wallet can be an issue if your wallet is lost or stolen.
Storing Your Password in an Unprotected Document: It’s normal for users to make Word or Excel passwords lists. This isn’t a secure practice. The difficulty is, anybody who accesses your machine can open these documents.
Utilizing a dependable password manager can be a more secure choice to assist you with monitoring that multitude of passwords. Password managers use encryption and different means to keep your data safe.
Habit of Changing Gmail Password?
The subject of how frequently to change your password is controversial. Numerous security-minded of businesses and a few apps require regular password changes.
While the motivation behind normal password changes is acceptable, a few studies have shown that they are not exactly successful. That is on the grounds that most users don’t make totally new passwords when they change their passwords. All things considered, they essentially change their current password by adding or changing a character.
Experts recommend that picking a strong password is a preferred security strategy over regular password changes. Select a strong password to protect Gmail account.
Use Authentication
While trying to increase user security numerous apps have gone past passwords to authenticate the user. Here are some normal strategies to protect your Gmail account.
- Security Questions – Security questions are likely one of most older types of user authentication. They are frequently utilized for password recovery. The inherent issue with security questions is that they frequently request data that could be readily accessible through social media like your pet’s name or the name of your high school.
- Phone Codes-A newer authentication technique is to require the user to enter a randomly produced code that is sent to their phone when they sign in. The code is different each time. The drawback to this, obviously, is that the user should keep their phone with them to get to their account. This can be inconveniently designed for certain users.
- Hardware – This includes a physical device that should be connected to your computer to consider authentication.YubiKey for LastPass is a genuine illustration of a usb device that adds an extra login access step.
- Biometrics – Biometric identification replaces passwords with extraordinary physical characteristics, for example, fingerprint scans, retinal scans, and voice recognition. While this type of identification is experimental, its utilization is turning out to be increasingly normal. Consider the iPhone’s Touch ID included. A few specialists who accept biometric identification will replace passwords soon.
Pay attention to browser updates
You might consider browser and software updates as far as added features, and you’d be to some partially right. Yet, many updates additionally contain crucial security features that protect your Gmail account from viruses, malware, and even hackers.
That’s the reason you ought to install updates when they become accessible. Continuously ensure that you download your updates from a reputable source usually the maker of your software or browser.
Try not to share your Gmail passwords, Use Shared Inboxes
If your team utilizes a group email address, for example, info, sales, or support, different team members need admittance to it.
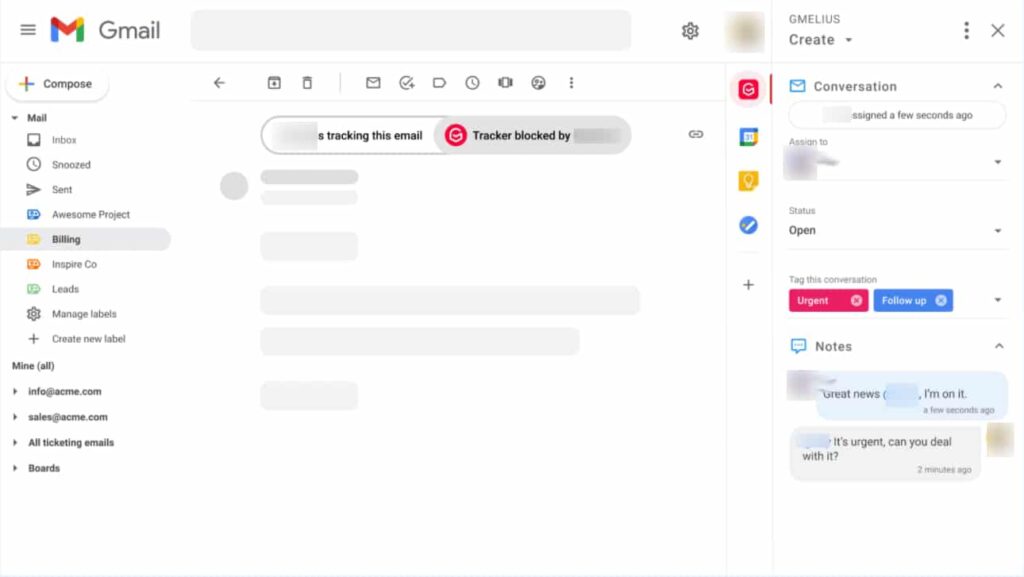
Sharing one password is a long way from being the most reliable solution. All things considered, the prescribed practice is to create shared inboxes for your group email addresses.
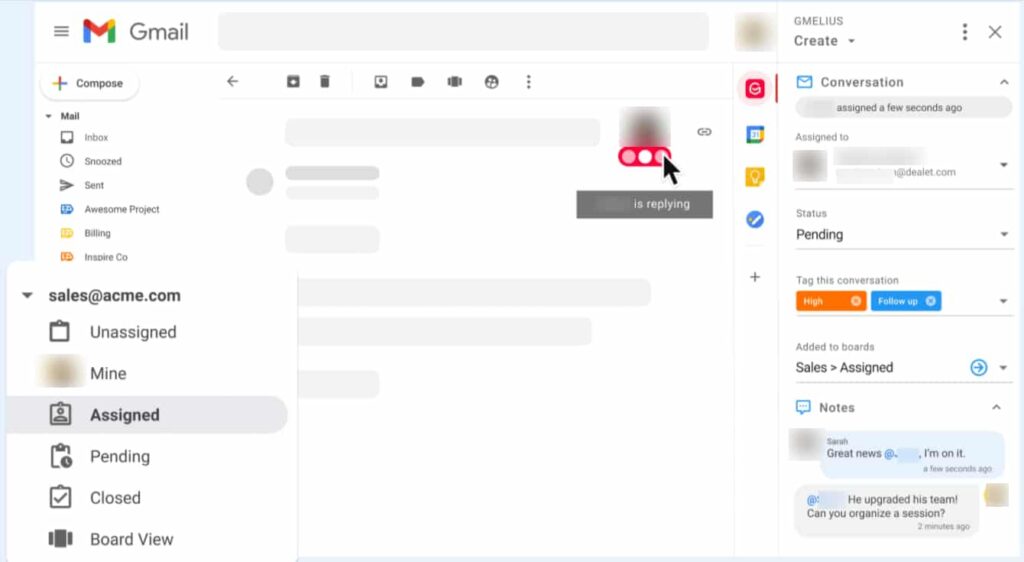
Shared Inboxes permit you to invite significant team members and let them manage group emails together directly from their separate inboxes. The best solutions available make it additionally possible to assign emails to specific team members, change the situation of a conversation, and add tags for more context.
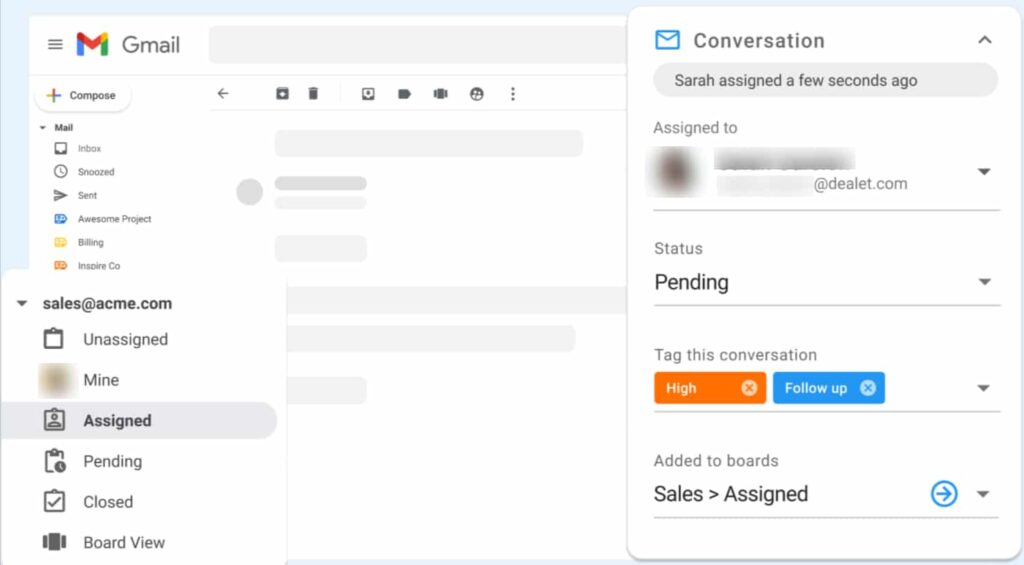
One more advantage of the shared inbox model is that your group can forget copy and collide replies. Teammates will see every other avatar if they are seeing an email, and the red ellipsis will beat continuously if they are replying.
Access to 3rd Party Apps
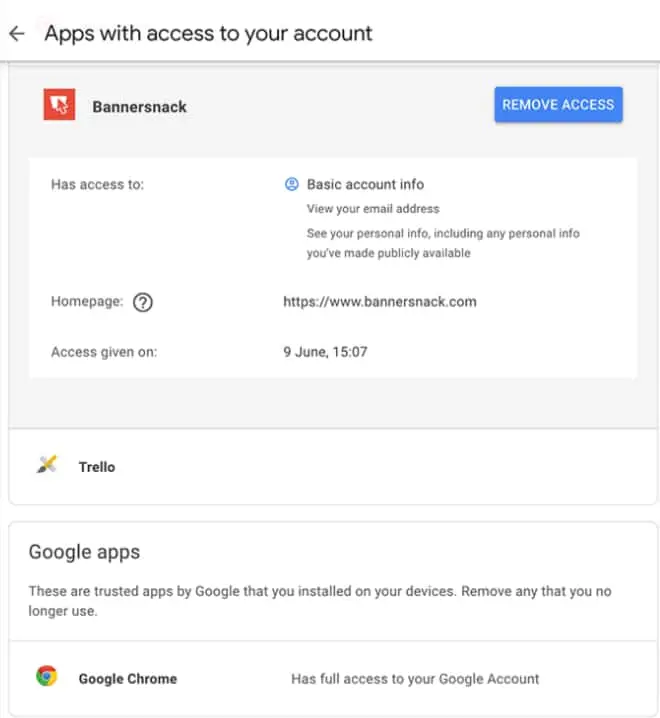
You might have signed up to a specific website utilizing your Google certifications or installed third-party extensions/apps over the long run. A portion of those might put your Gmail account at risk one day. The best practice is to consistently revoke access to apps you at this point don’t use to mitigate any risks.
Head to your Googles account authorizations page to revoke access to anything you don’t need to keep. Ensure to repeat this progression occasionally, e.g., once quarterly.
Check doubtful activity
If Google notices doubtful activity in your account they’ll send you a notification. It very well might be that there are sign-ins from a new area or a new device. In a perfect world, you ought to likewise manually review your account in some measure once per month to ensure that no doubt has taken place.
To review your account, click on the link ‘Details‘ situated on the right-hand side of the footer of your mailbox.

Check your account filters for forwarding emails
It’s significant that you ensure that there are no dynamic filters in your account which might be sending your email to a third-party email address. This check is basic: Go to your Gmail Settings page and snap on the Filters tab. Search for filters you haven’t authorized or don’t utilize and delete them.
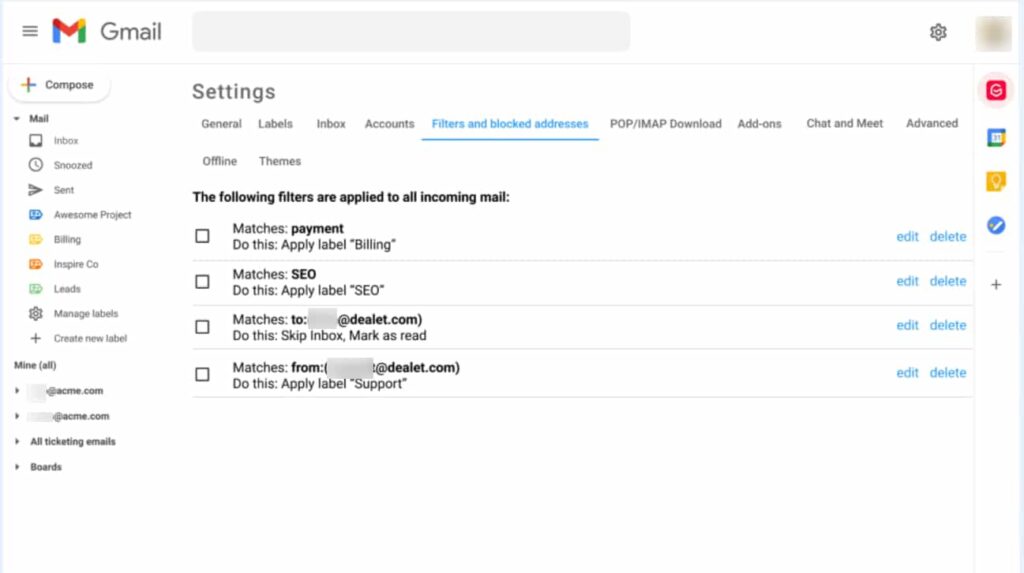
Furthermore, check the Forwarding and POP/IMAP tab to guarantee there’s no unapproved sending address other than those approved by you.
Authenticate your emails when sending sensitive information
On receiving an email, you might see that close to the sender’s email address there’s a little red padlock. This indicates that the message is conceivably unsafe.
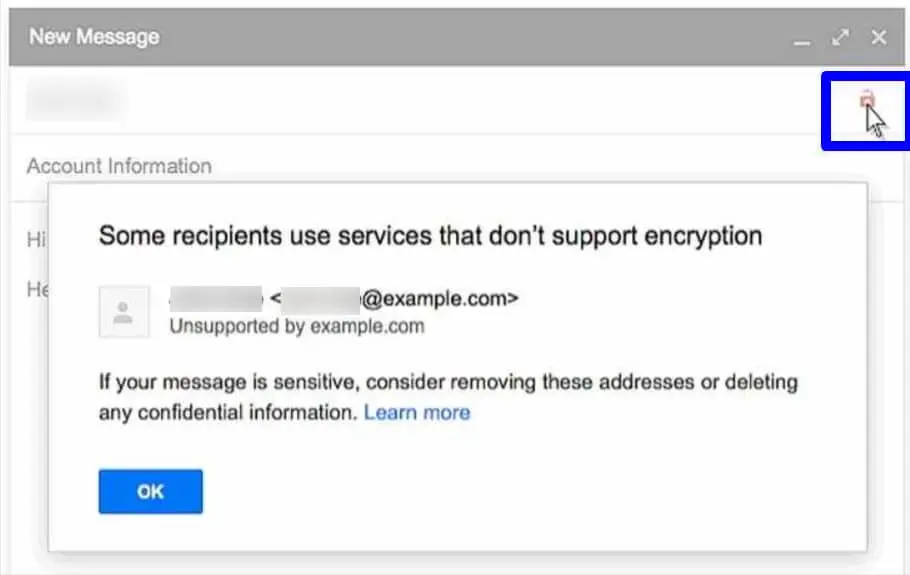
This red unlocked symbol accompanies emails that have not been verified by Transport Layer Security (TLS) encryption. Try not to stress excessively if you’re not sure how the technology works. You possibly should be concerned if you see this symbol and the message has something to do with passwords or other sensitive data. Now you really want to contact the sender of these insecure emails if need to keep trading messages with this person.
Detect and block email trackers
You may not know that many people and companies track emails they send these days. With this data, they might know precisely when, where, and how often you’ve read their message. You can detect and block such trackers by installing expansions. We prescribe to utilize our own tool to achieve this as we probably are aware our code is clean and we don’t store nor transmit your Gmail data.
Gmail Security
Change Your Gmail Password
- Start from the main Gmail inbox screen
- Snap the arrow close to the Settings icon on the upper right corner to display the drop-down menu:
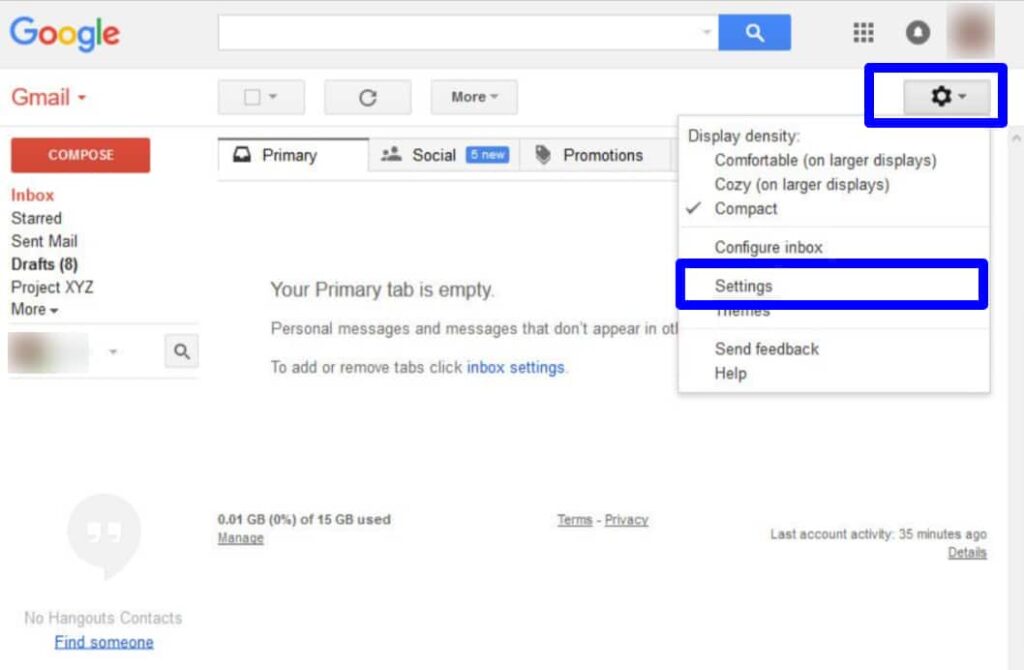
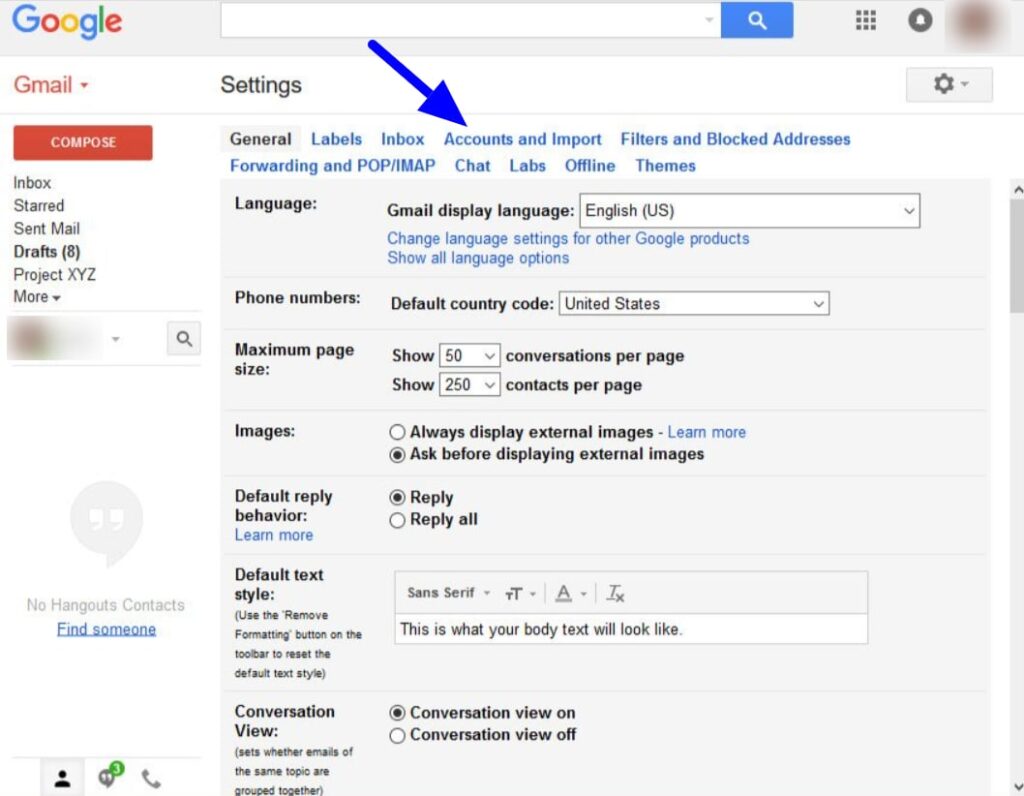
- Snap the Settings choice to display the Settings screen:
- From the menu across the highest point of the screen, select the Accounts and Import choice. You will see that the choices on the Settings screen change:
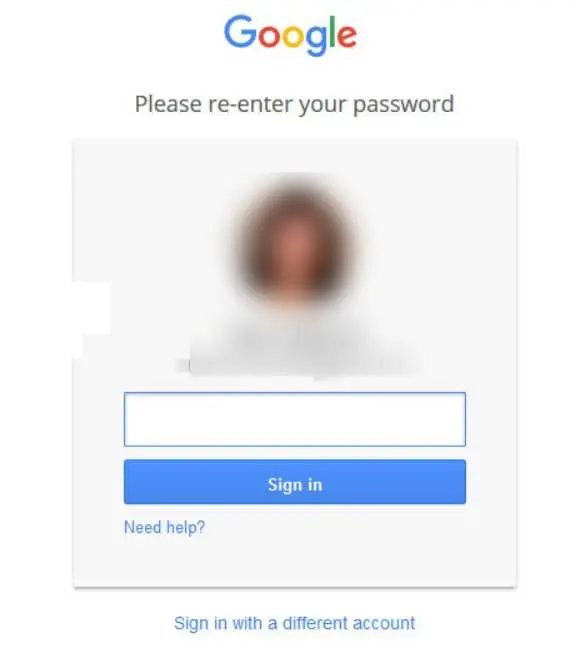
- Under the Change account settings category, select the Change password choice. You’ll be prompted to re-enter your current password”.
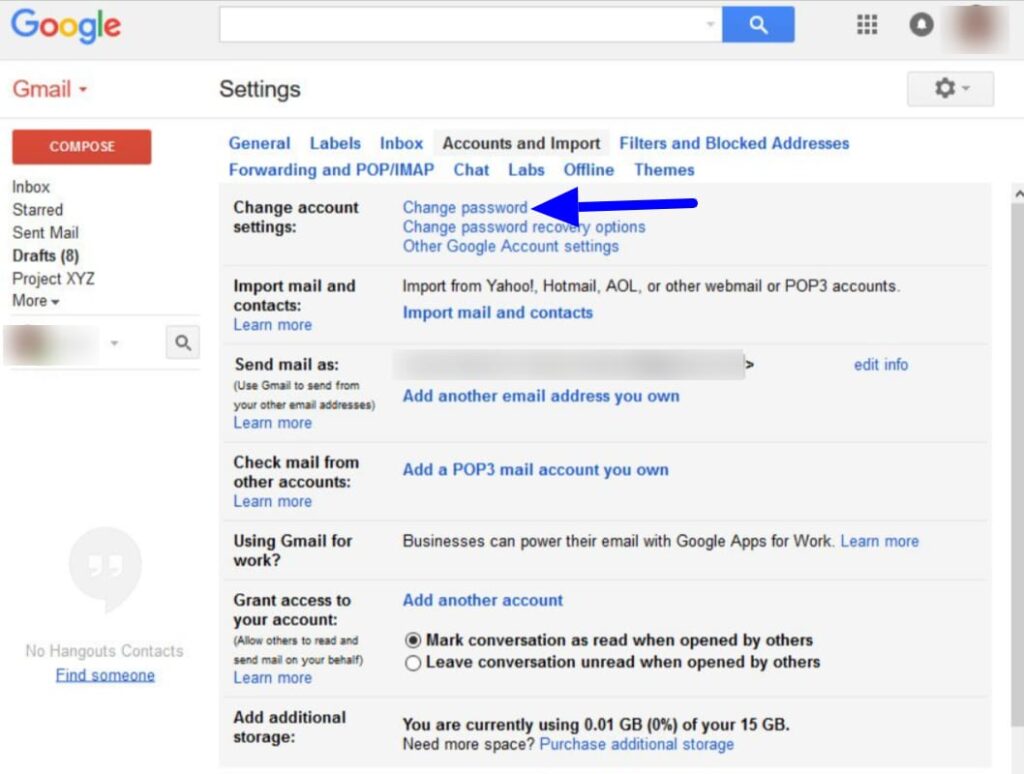
- Type in your present password, and hit the Sign in button.
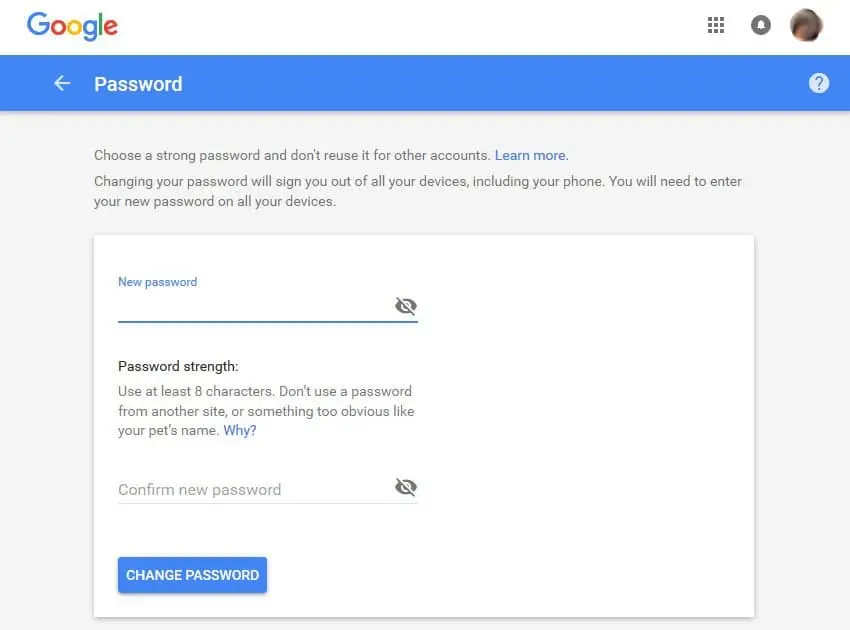
- The Change Password screen appears:
- Type another password below the New password field. Give specific consideration to your password strength. Type the new password one more time in the Confirm new password field.
- The passwords should be identical. Enter the Change Password button when you are finished.
- You will get a brief prompt that your password was changed. The Sign-in and security screen displays, where you can make other security changes:
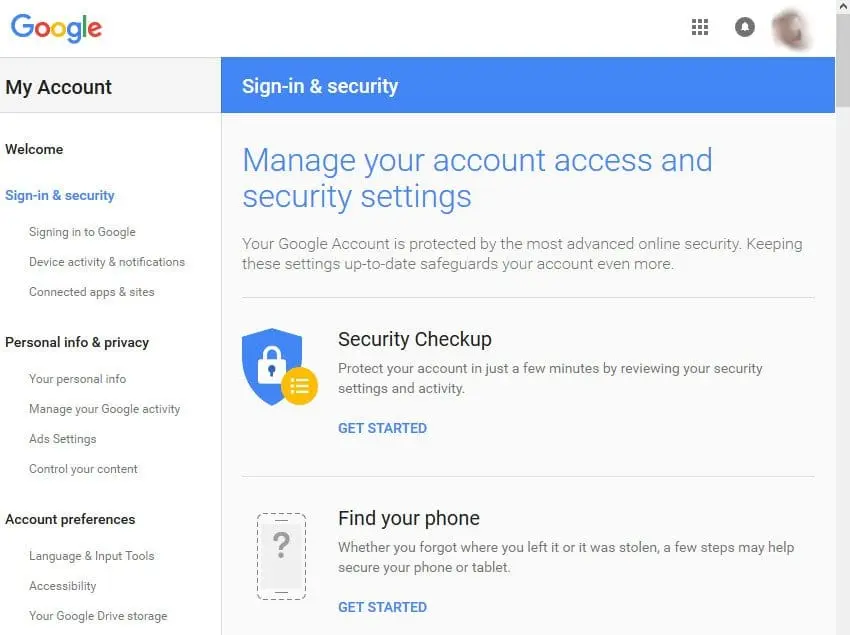
Check Your Security Settings
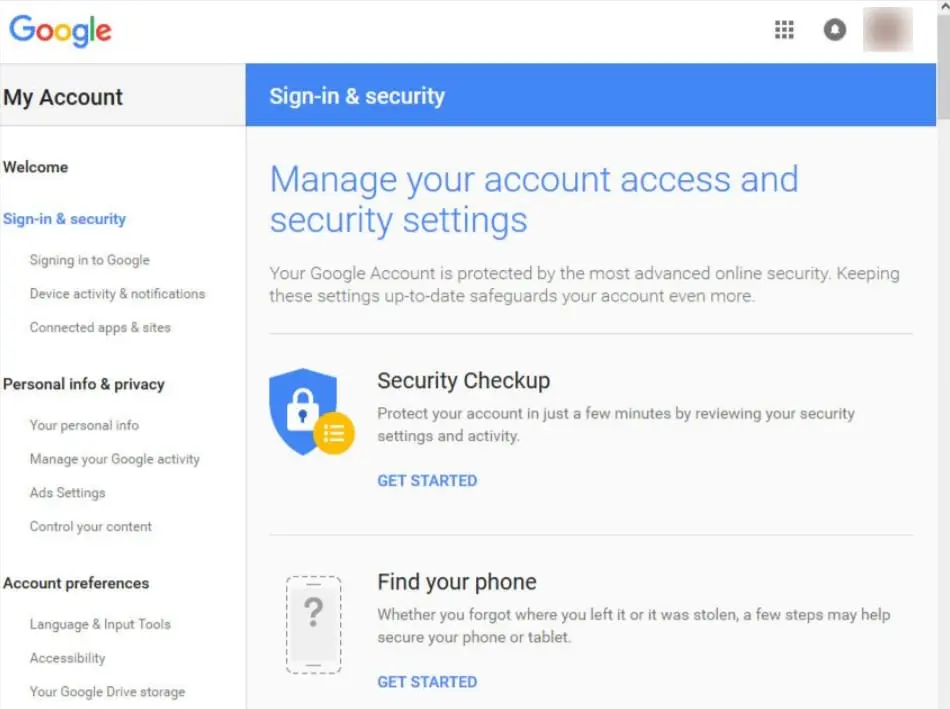
- If you’ve quite recently changed your password, you are as of now at the Sign-in and security screen.
- If you are not at the Sign-in and security screen, enter on your photo in the upper right of the primary Gmail interface. A pop-up displays showing your Google account data:
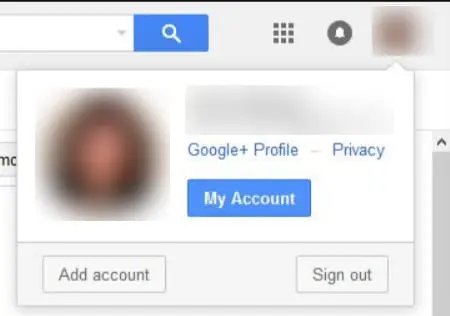
- Hit the My Account button.
- The My Account screen appears:
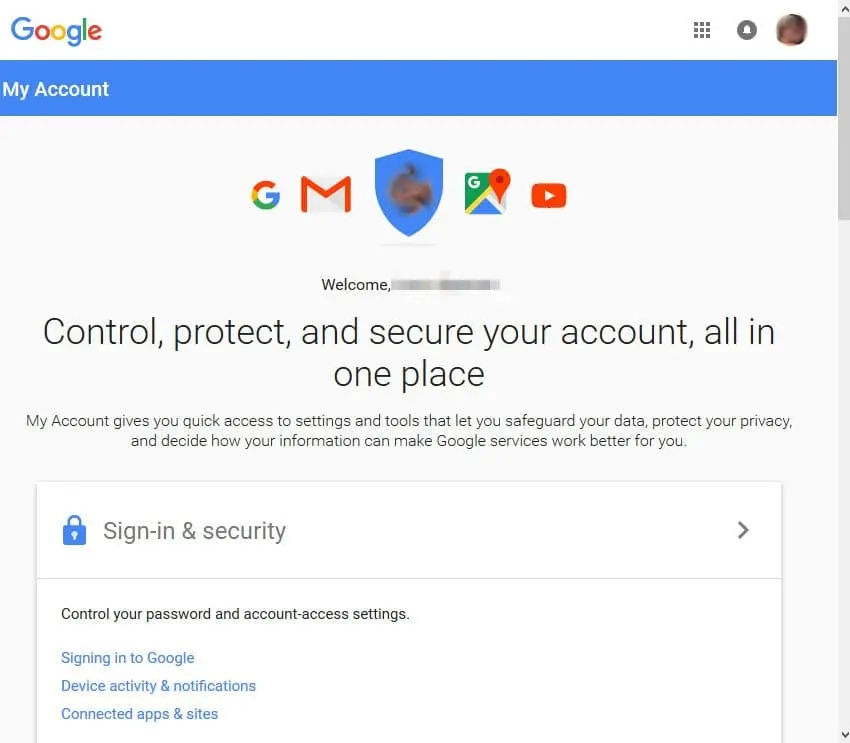
- Hit the Sign-in & security option.
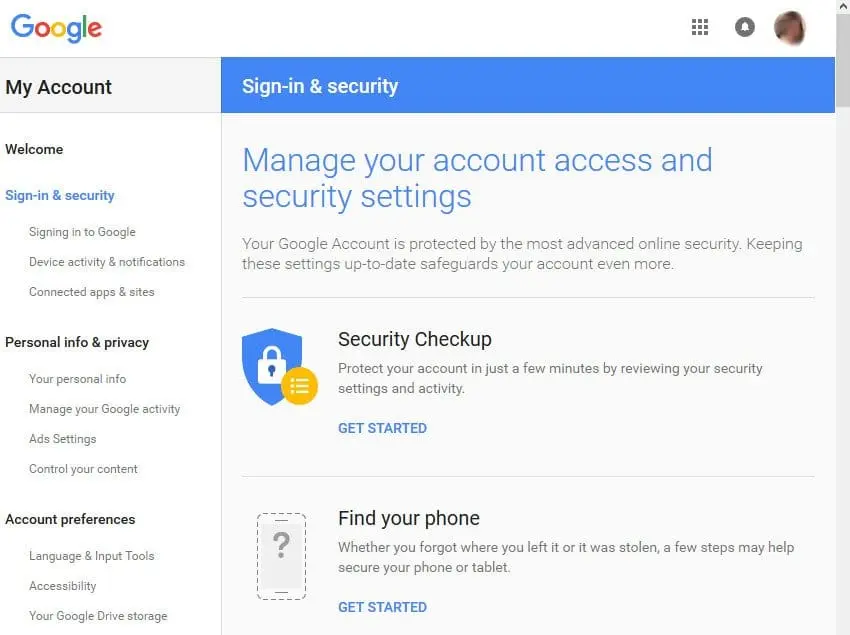
- The Sign-in & security screen displays:
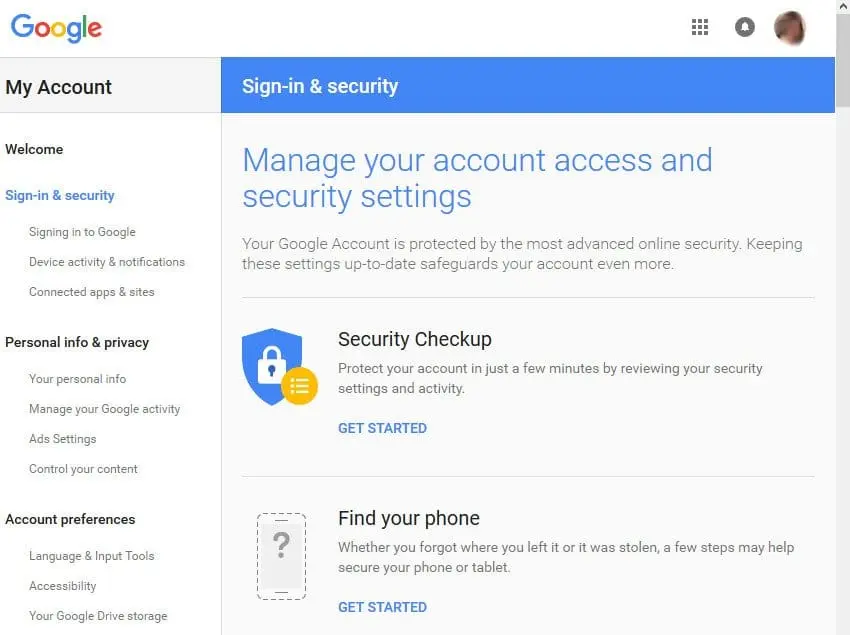
- This is the screen you use to really look at your current security settings. Utilize the scroll bar on the right of the screen to drop down through your settings.
- You will see there are three categories covered on this screen:
- Signing in to Google
- Device activity and notification
- Conected apps and sites
- Your present status in every one of these areas is displayed on the screen. Review the status with each field in every category carefully.
- Make changes to your security settings from this screen by tapping the arrow to one side of each field. You might be prompted to enter your password before you can make the change.
- Presently how about we investigate one of the fields: 2-Step Verification
2 Step Verification
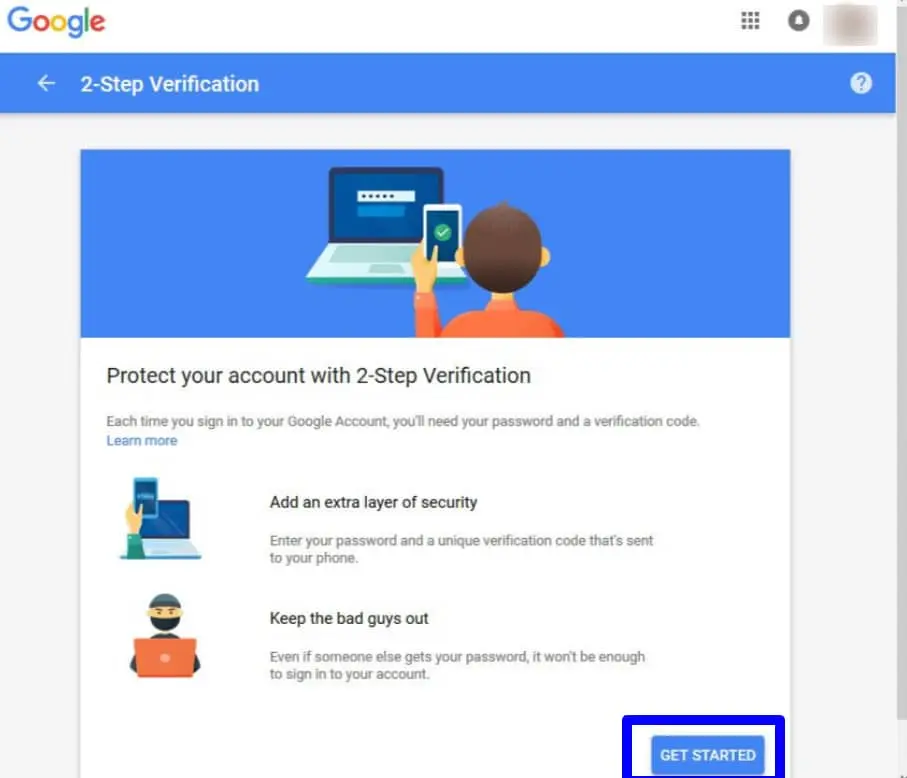
It’s nice to turn on 2-Step Verification if you haven’t effectively done it. It adds an additional layer of protection to your login process. For this situation, the additional layer is a phone code.
Each time you sign in to a Google account you will get a unique code by phone. You should enter that code before you can get to your account.
- Begin at the Sign-in & security screen.
Look down to find the 2-Step Verification field under Password and Sign-in Method.
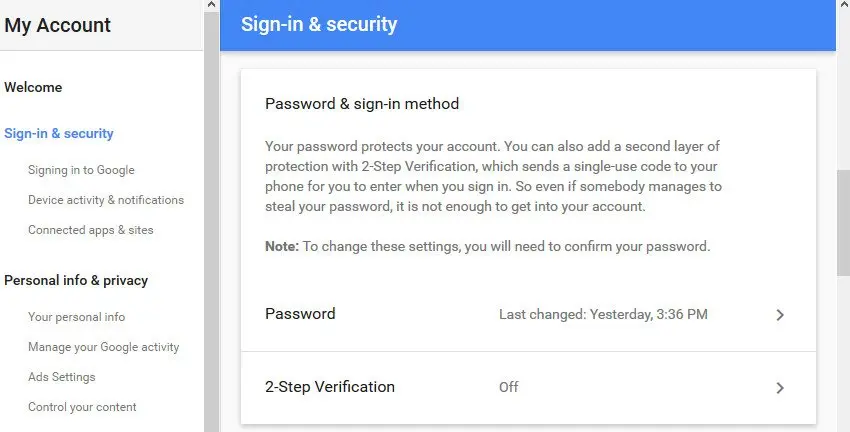
- Snap the arrow to right side of the 2-Step Verification field. The informative 2-Step Verification screen displays some data about the significance of 2-step verification:
- Snap the Get Started button.
- You will be prompted to enter your password. After you type your password, the 2-Step Verification window appears with two inquiries:
- Answer the questions. Type the phone number where you need to get verification codes. Select whether you need to get the codes by text message or call.
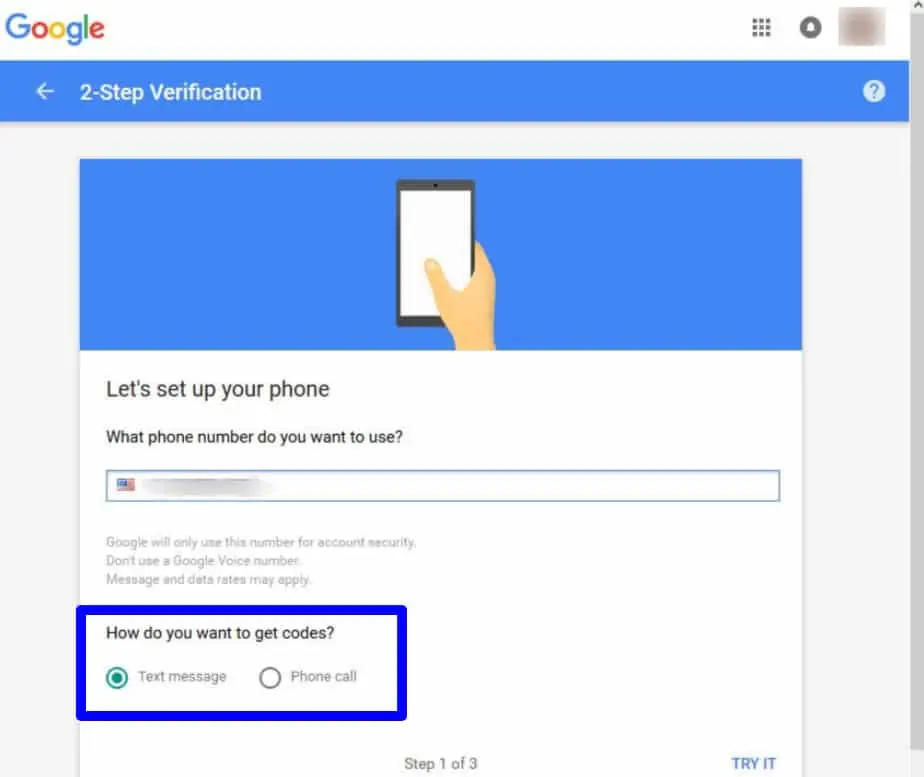
- At the point when you have answered the questions, enter on the Try It button. Google quickly sends a code to your phone. You are prompted to enter the code into the screen to proceed:
- Type the code you got. Snap Next in the lower right corner of the window.
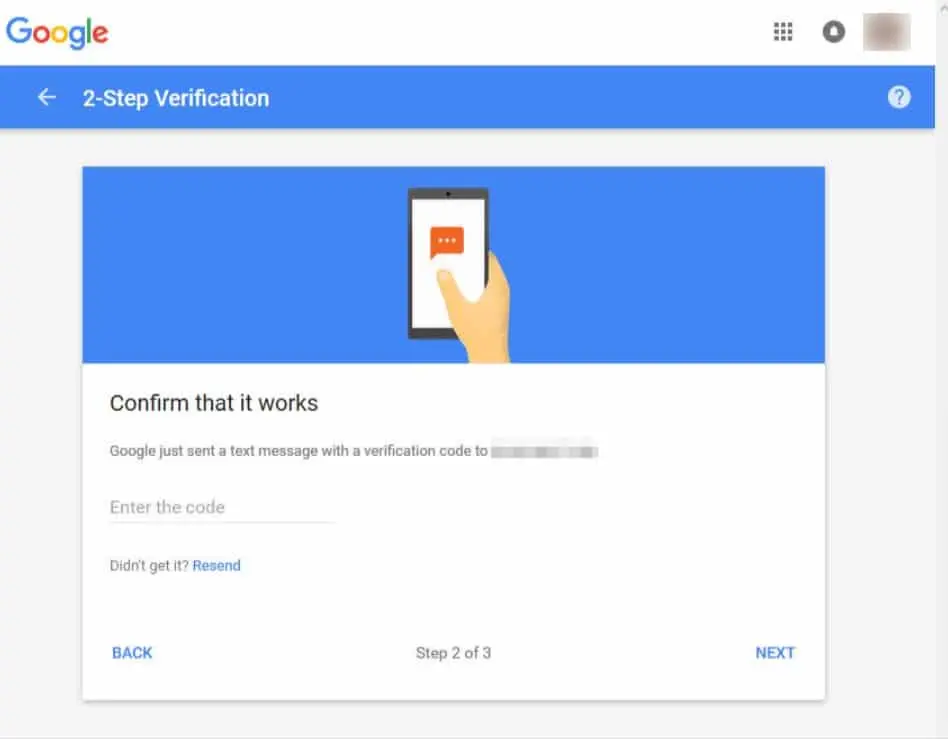
- If you effectively entered the code, you are prompted to turn on 2-step verification. Hit the Turn On in the lower right corner of your screen to turn it on. You are prompted to enter your password once more.
- Type your password and enter on the Sign in.
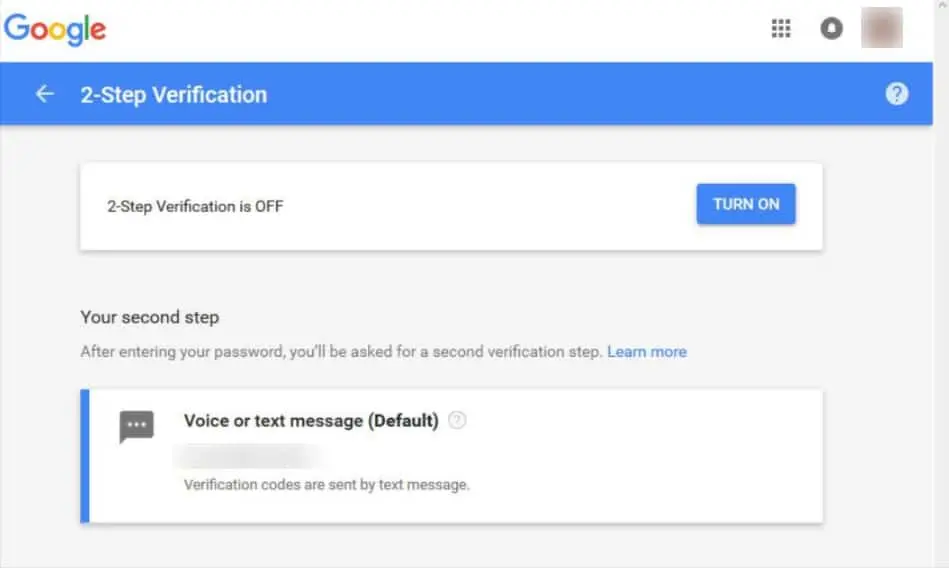
- Another screen displays requesting that you verify your choice to turn 2-step verification on:
- Snap the Turn On button in the upper right of the screen. Two-step verification is turned on.
- The Sign-in and security screen is updated to reflect that it is on.
Recovery Options for a Lost Password
You can change your settings so that there are two different ways to recover a lost password. I will go over the two techniques.
- Start from the Sign-in and security screen:
Utilize the scroll bar on the right side of the screen to look down to the Account recovery options.
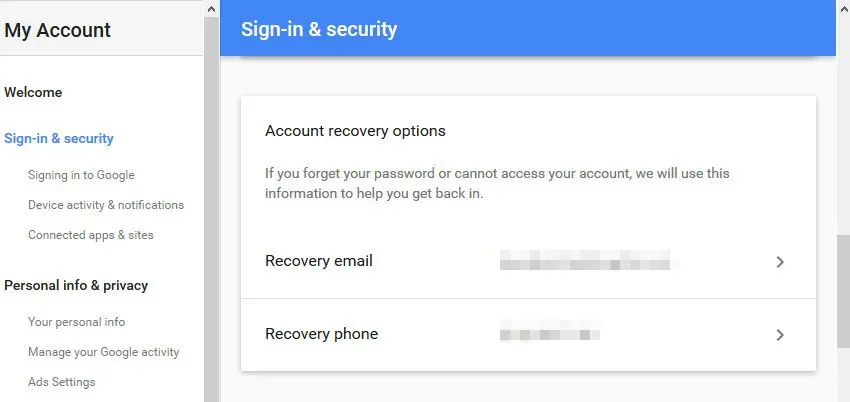
- There are two account recovery choices:
- phone
- You can set up a recovery email and a phone from this screen. How about we start by setting up a recovery email.
- Snap the arrow to the right of the Recovery email field. You are prompted to hit your password.
- Type your password and afterward hit the Sign in.
- Since we set up 2-step verification prior, the system sends you a verification code. Enter the verification code you were sent and snap the Done.
- You are prompted to enter your recovery email:
- Type your recovery email address, then at that point Snap the Done button in the lower right of the brief.
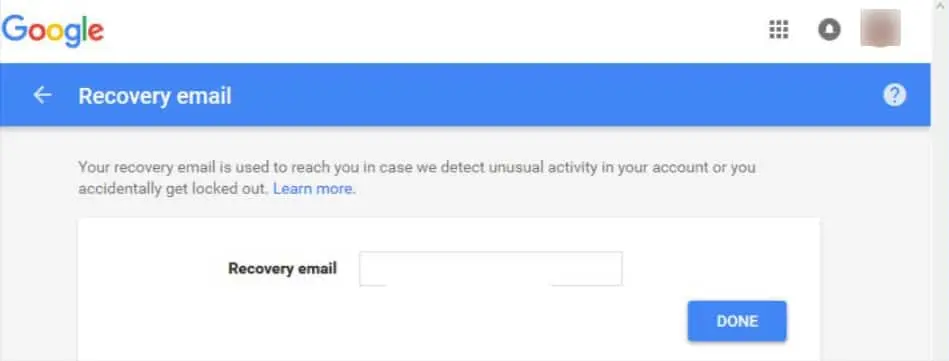
- Your recovery email is set. The system gets back to the Sign-in and security screen.
- Presently the time has come to set up your recovery phone. Look down to the Account recovery options.
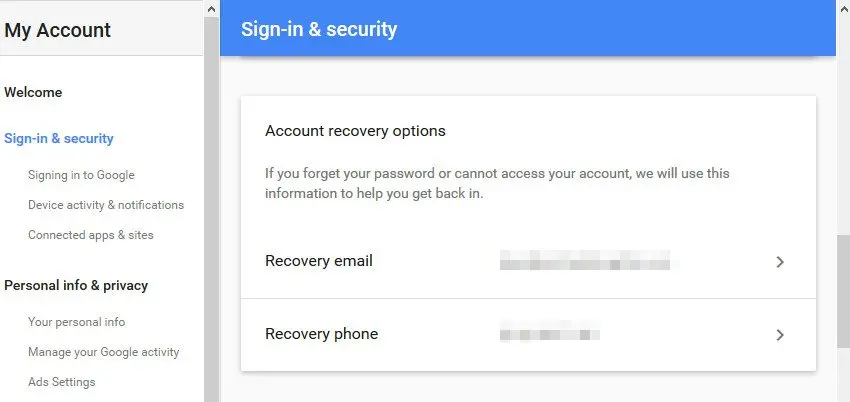
- Hit the arrow on the right of the Recovery phone field. You are incite to enter your password. Type it in and hit on the Sign In.
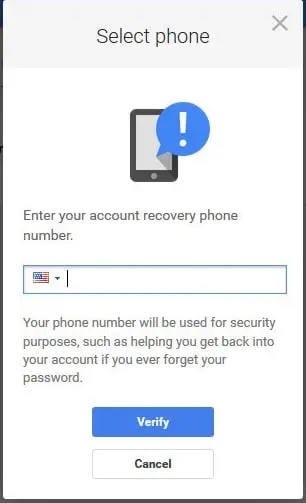
- You are prompte to hit your recovery phone:
- Enter on the Add recovery phone.
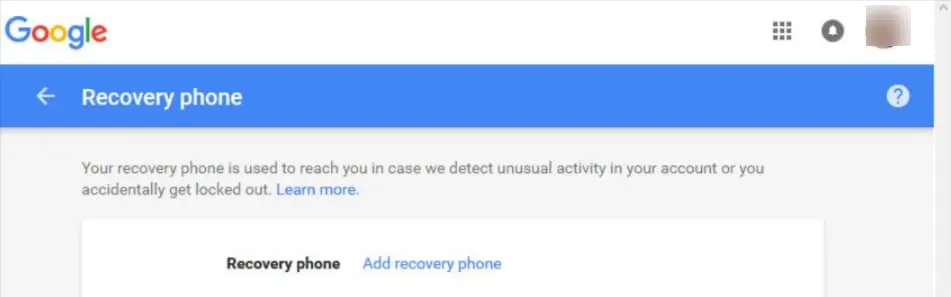
- If you have entered a phone number in your account before, you can choose it from the following brief. Or then again, type in another phone number on the following screen:
- If you are entering another phone number, enter Verify when you are done. Follow the prompts to check your new number.
- Your recovery phone is set. The system gets back to the Sign-in and security screen.
Conclusion
Online tricks are just about as old as the internet itself and have evolved over the decades of the very long time alongside it. Hackers and cybercriminals are persistently trying new techniques to suck in and stunt users into uncovering their huge personal information. The absolute most normal hacker attempts to revolve around breaking email services like Gmail.
Each several months, Google experiences some type of large scale hacker attack. Also that hundreds, even a great many people get their account breaches every day. In any case, despite the fact that this is a stressful statistic, there are a few things you can do to protect your Gmail account.