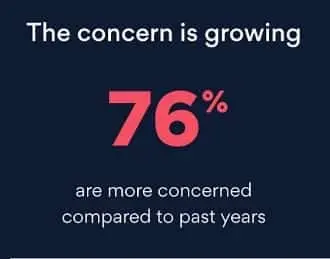
Social media hacking is the act of aiming to adjust the results of social behaviour through coordinated efforts. Fears of social media hacking are increasing globally daily. Everybody is aware of social media’s numerous risks to privacy and security.
The term “social hacking” refers to planning and carrying out coordinated acts to influence social behaviour. The main goal of social hacking is to enter a physical area and a limited piece of data without the required authorization. There are multiple causes for concern, including the disclosure of your private details and the rising frequency of social media scams.
These fears are understandable given that most of those polled said they knew someone who had been a tragedy of social media hacking.
And now, a new NordVPN survey has revealed that 7 in 10 Americans are scared that their social media profiles may be hacked, with nearly a third expressing a high fear.
What will you see here?
Human error
Mistakes are familiar to everyone. In today’s hectic environment, it is too simple for a worker to expose the business to internet dangers. In reality, the EY Global Information Security Survey found that “employee vulnerability” was to blame for 20% of hacks.
Online tests and tasks can occasionally be challenging. Employees may unintentionally cause social media security problems by completing them.
It can seem fun when you see postings like “learn your elf name” and “10-year challenge.” they can. However, provide fraudsters access to data typically used in password stealing. The AARP published a warning about these sorts of tests to make its target audience of older internet users aware of the problem.
Social media platforms with the high and low reliability
The youth have spoken, and what is their opinion? Twitter & youtube are the less popular social media networks.
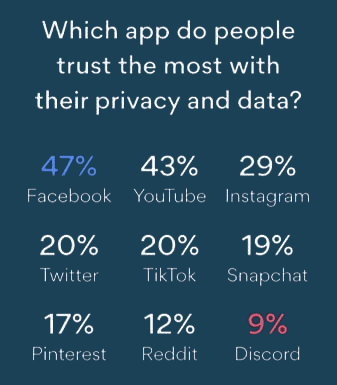
The concern over being hacked “coincides with an overall lack of confidence in social media,” according to NordVPN, which also looked more closely at which social media applications users trust the most. 35% of respondents stated it was their favourite app, with 26% for TikTok & 32% for Instagram. One of them enquired about their favourite social media platform, and Snapchat won.
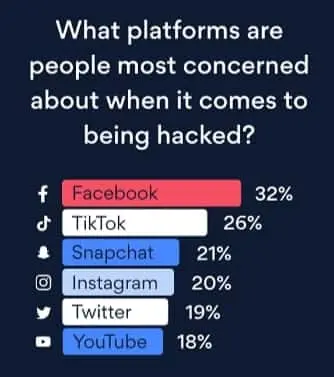
Regarding the least trustworthy social media applications, Facebook claimed the top rank with 32%, followed by TikTok at 26% and Twitter at 19%.
Imposter accounts of Social media hacking

An impostor might quickly construct a social media acct that appears to be associated with your business. This is one of the key benefits of obtaining social network verification.
Imposter accounts of Social media hacking were dealt with in just six months. Ninety-five per cent of those accounts had access to the system immediately restricted at registration. However, more than 67,000 phoney accounts weren’t dealt with until users reported them. According to Facebook, around 5% of monthly active user accounts are false.
False accounts may target your clients or potential employees. When your contacts are duped into revealing private information, your image suffers. Recently, the Cayman Islands’ government was forced to issue an impostor notice. On Instagram, someone was posing as a government minister.
Social Engineering attacks
Generally, “social engineering” describes various malicious behaviours through interactions with others. It uses psychological trickery to persuade people to breach security or disclose private information. It is one of the vital points of Social media hacking. Social engineering assaults take multiple forms and can be carried out anywhere there is a social connection. The following are the leading Social Engineering attacks Scareware, Phishing, Baiting, pretexting, and many more.
If an attacker aims for a high-stakes payoff, the most accessible approach to swiftly obtain monetary incentives for their efforts is to target companies. An attacker may start by searching LinkedIn for potential targets. Targets might include high-level business personnel and individuals with minimal privileges who could be duped into giving extra company information or fall for a phishing attempt that provides the attacker access to the account credentials.
According to the response of the technical director, malicious individuals seldom attempt to attack technical flaws in Windows. Instead, they’re chasing you, finding one individual who could be inclined to accept an attachment containing harmful stuff that doesn’t require as much technical expertise. Only approximately 3 percent of the malware they come across tries to take advantage of a bug in the software—the other 97% attempt to deceive a user through some form of social engineering method. Therefore, whether your workstation is a Mac or a Personal computer makes no difference.
Security
The hackers could enter Target’s network indirectly by finding a third-party firm. That had access to Target’s credentials, although Target may not have been lax in its security. The social hack involved tricking third-party employees into disclosing personal information, whereas the cybercrime used an email phishing scam that contained malware. Cyberattacks against large firms like Target, other international companies, and busy websites underline the necessity for careful internet security. Due to the inadequate security protection that is assumed to be in place on tiny websites, they are much more susceptible to assaults. Target’s third-party mechanical business lacked proper security software, leaving them vulnerable to a malware assault.
Ways to stay safe from Social Media Hacking.
Social media nowadays are used for various business purposes also. So compromising its data to any hacker can harm your business as they get whole data regarding your business. However, there are ways to safeguard your social media accounts from these hackers and live without any headaches. The following ways are:
Set Strong Password

One of the basics that we can cover is by setting up a strong password which is difficult to crack by hackers. One can create strong passwords by combining Uppercase letters, Lowercase letters and setting up Alphanumeric passwords. Most people don’t know the value of setting a strong password until the password is compromised. However, you should set up a strong password which will prevent you from any harm caused by the hacker.
Turn on Two Factor Authentication
Nowadays, every social media provide two factor authentication system. If you don’t know what it is, it enables two step to verify that the authorized person is logging in. First it verifies the password and in second step it asks for the code send via text or email to the account holder. So it is quite a useful way to avoid any invasion by other.
Use genuine third party apps
Currently there are various apps that compliments social media apps like posts scheduler, follower manager etc. which requires your login details. It’s harmful to provide such credentials as there are high chance that your data can breach or they use it for harmful purpose. So before using such third party apps make sure that they are genuine and your data is safe with them. It’s better to avoid such apps but if you are using them make sure to verify it.
Install Antivirus Software

Make sure you have Antivirus software install in your device which can tackle such hacking or data breaching. Many sites itself provides protection against such harm but installing antivirus software will give you peace of mind. We recommend you install pro version of any antivirus, but if you are low on budget than free version will also do.
Save password in password manager
If you are suffering from the problem of forgetting your password like most others, then you can save your password in password manager. Now as we said earlier to set up strong password, its quite a stress to remember such passwords and entering them again and again. So to solve this problem, one can use password manager to save their password. The most recommended for this task is Lastpass.
Why do hackers target social media?
The main goal of social hacking is to enter a physical area or a little piece of data without the required authorization. Most social hacking attacks are carried out by impersonating a person or group known to the victims, either directly or indirectly.
Can social media be hacked?
Social media hacks are Avoidable. Hacks of social media accounts happen more frequently than one may imagine. However, you may take proactive measures to reduce your risk of experiencing them.
How do hackers categorize you?
They frequently search across social networks to find high-potential targets, then learn more about them by looking through their public profiles for information on their background, employment, hobbies, and interests.
How are individuals get breached?
Due to the fear of social media hacking, Many individuals create memorable passwords for their phones and computers but often forget to do the same for their Internet routers and other smart devices.
Conclusion
Social media safety is more crucial than ever due to the rising usage of social technologies for corporate communications.
More users are concerned about having their social media profiles hacked. This is not unexpected, given that most respondents said they knew someone who had been a victim of a social media breach. However, 28% of those polled stated they knew 5–10 people who had their social media accounts hacked.